The Promise and the Pitfall
Infrastructure as Code (IaC) was supposed to be our salvation. The promise was simple, beautiful, and compelling: define your servers, networks, and databases in declarative configuration files. Version them, review them, and deploy them with the same rigor as application code. Terraform, with its provider ecosystem and declarative HCL syntax, became the undisputed champion of this movement. Teams everywhere rejoiced as they tore down manual click-ops and embraced the single source of truth. But a quiet, insidious problem has been growing in the shadows of our version-controlled main.tf files. We’ve fallen into a trap—not of IaC itself, but of its incomplete implementation. Your Terraform scripts aren’t just failing you; they’re lulling you into a false sense of security while technical debt accrues at the infrastructure layer.
The Illusion of Control
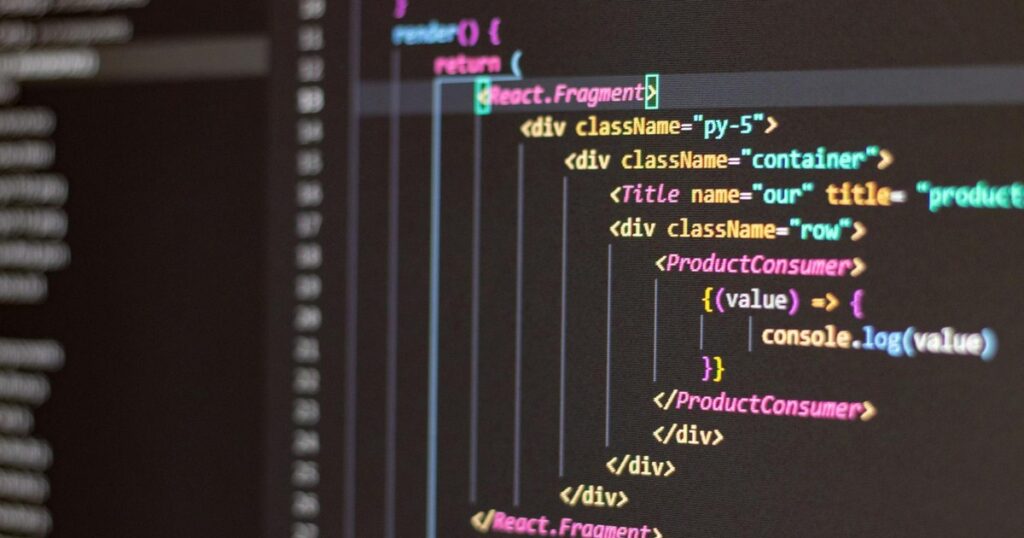
You run terraform plan and get a neat, predictable output. You see the green pluses and red minuses, a comforting ledger of what will change. You apply, and the infrastructure converges. The trap is believing this is the whole picture. In reality, this is merely the initial state of your resources. What happens after Day 1 is where the illusion shatters.
The Drift Dilemma
Infrastructure drift is the silent killer of IaC integrity. A well-meaning engineer logs into the AWS console to quickly restart an instance. A midnight emergency fix involves manually adjusting a security group rule. A third-party service auto-scales a component outside of Terraform’s purview. Suddenly, your Terraform state file—that supposed source of truth—is a historical document, not a current blueprint. The next terraform apply could be a destructive surprise, reverting a critical hotfix or, worse, destroying a resource it no longer recognizes. The tool meant to enforce consistency now introduces unpredictability.
The Monolithic Configuration Monster
We took the “as Code” part seriously but forgot the architecture part. A single, gargantuan Terraform root module containing your entire VPC, Kubernetes clusters, databases, and monitoring tools is not a victory. It’s a liability. This pattern creates:
- Terrifying Blast Radius: A typo in a storage module can trigger a cascade of unrelated changes.
- Plan Paralysis: Running
terraform plantakes 20 minutes, discouraging frequent, small iterations. - Team Collision Hell: Multiple teams waiting on a locked state file, unable to work independently.
You’ve traded the spaghetti of manual processes for the rigid concrete of an unchangeable monolith.
The Statefile: A Single Point of Failure
Terraform’s central innovation—and its greatest vulnerability—is the state file. This JSON file maps your configuration to real-world resources. We store it remotely (in S3, usually) with locking, patting ourselves on the back for best practices. But this setup is fraught with peril.
- Corruption Catastrophe: A corrupted or partially applied state can leave you in an unrecoverable limbo.
- Secret Spillage: Sensitive outputs are often stored in state in plaintext, a massive security oversight.
- The “taint” and “import” Dance: When reality and state diverge, you enter the manual, error-prone ritual of tainting and importing resources, a process that feels suspiciously like the click-ops we sought to escape.
The statefile becomes a brittle anchor, tethering your infrastructure to a fragile artifact.
Missing the “Ops” in “DevOps”
DevOps is a culture, not just a set of tools. Yet, many teams treat Terraform as a “fire-and-forget” deployment tool. They lack the operational practices to make IaC sustainable.
No Testing Strategy
Would you push application code without unit or integration tests? Of course not. But teams routinely apply Terraform changes to production with zero testing beyond a plan output. Where are the:
- Compliance Guards: Tests ensuring no S3 bucket is ever configured for public read?
- Cost Regression Checks: Automated analysis flagging a change that will spin up fifty
m5.24xlargeinstances? - Integration Validation: A post-apply smoke test verifying the new ALB actually returns a 200 OK?
Without these, you are merely automating negligence.
Poor Code Hygiene
Terraform code is often treated as a second-class citizen. It’s littered with hard-coded values, lacks consistent code style, and has no meaningful review process. Variables are misused, modules are duplicated, and the locals {} block becomes a dumping ground for inscrutable logic. This isn’t “as Code”; it’s “as Config Spaghetti.”
Climbing Out of the Trap: A Path to IaC Maturity
Recognizing the trap is the first step. Escaping it requires a shift in mindset and practice. Here’s how to turn your failing Terraform scripts into a robust, reliable foundation.
Embrace Modularity and Composition
Break the monolith. Structure your Terraform code like you structure your application: with purpose-built, reusable modules. A well-designed module has a clear interface (input variables and outputs) and a single responsibility. Use a composition pattern (like the Terraform stack pattern) to weave these modules together for specific environments (e.g., staging, production). This reduces blast radius, speeds up plans, and enables team autonomy.
Implement GitOps for Infrastructure
Treat infrastructure changes like application changes. Use a pull request-driven workflow. Every change to the main branch should be via a PR that triggers:
- A
terraform planwith the output attached to the PR for review. - Automated policy checks (using tools like Open Policy Agent or Terraform’s own Sentinel/OPA).
- After merge, an automated, monitored apply from a CI/CD pipeline (not a developer’s laptop).
This enforces review, provides an audit trail, and eliminates configuration drift at its source.
Harden Your State and Security
Go beyond remote state. Enable state file encryption at rest. Use a backend that supports robust locking (like Terraform Cloud/Enterprise or a DynamoDB table for S3). Most critically, never store secrets in Terraform outputs or variables. Integrate with a secrets manager (HashiCorp Vault, AWS Secrets Manager) and fetch secrets dynamically at runtime.
Test, Validate, and Monitor
Build a testing pyramid for your infrastructure.
- Unit/Static Tests: Use
terraform validateandtflintfor syntax and basic linting. - Contract Tests: Validate that your modules produce the expected outputs for given inputs.
- Integration Tests: In a short-lived, isolated environment, run a full
terraform applyand use tools liketerratestto verify the actual cloud resources behave as intended. - Drift Detection: Run automated, periodic
terraform planjobs (e.g., nightly) to detect and alert on any configuration drift, so you can remediate proactively.
Document the “Why”
Complex infrastructure decisions—why this subnet mask, why this particular instance type—get lost in time. Embed this context using meaningful variable names, descriptive comments in code, and ADRs (Architecture Decision Records) in your repository. Future you will be grateful.
Conclusion: From Trap to Foundation
Infrastructure as Code, and Terraform specifically, are not failures. They are powerful, essential tools in the modern cloud arsenal. The trap isn’t in the tool, but in the half-measure. We adopted the syntax but neglected the discipline. We automated provisioning but ignored lifecycle management. By moving beyond the initial allure of declarative files and embracing the hard work of modular design, rigorous testing, GitOps workflows, and operational vigilance, we can escape the trap. Your Terraform scripts shouldn’t be a fragile set of instructions; they should be the living, tested, and trusted foundation upon which your entire application is built. Stop letting them fail you. Start engineering them.